The Ultimate API Authentication Guide for Beginners: Basic, API Key, JWT & OAuth 2.0 with Practical Examples, Framework Design & Interview Mastery
This API Authentication Guide will talk about how API Authentication is the backbone of secure API communication. If you are an automation tester, test lead, or QA architect, understanding authentication is not optional — it is foundational.
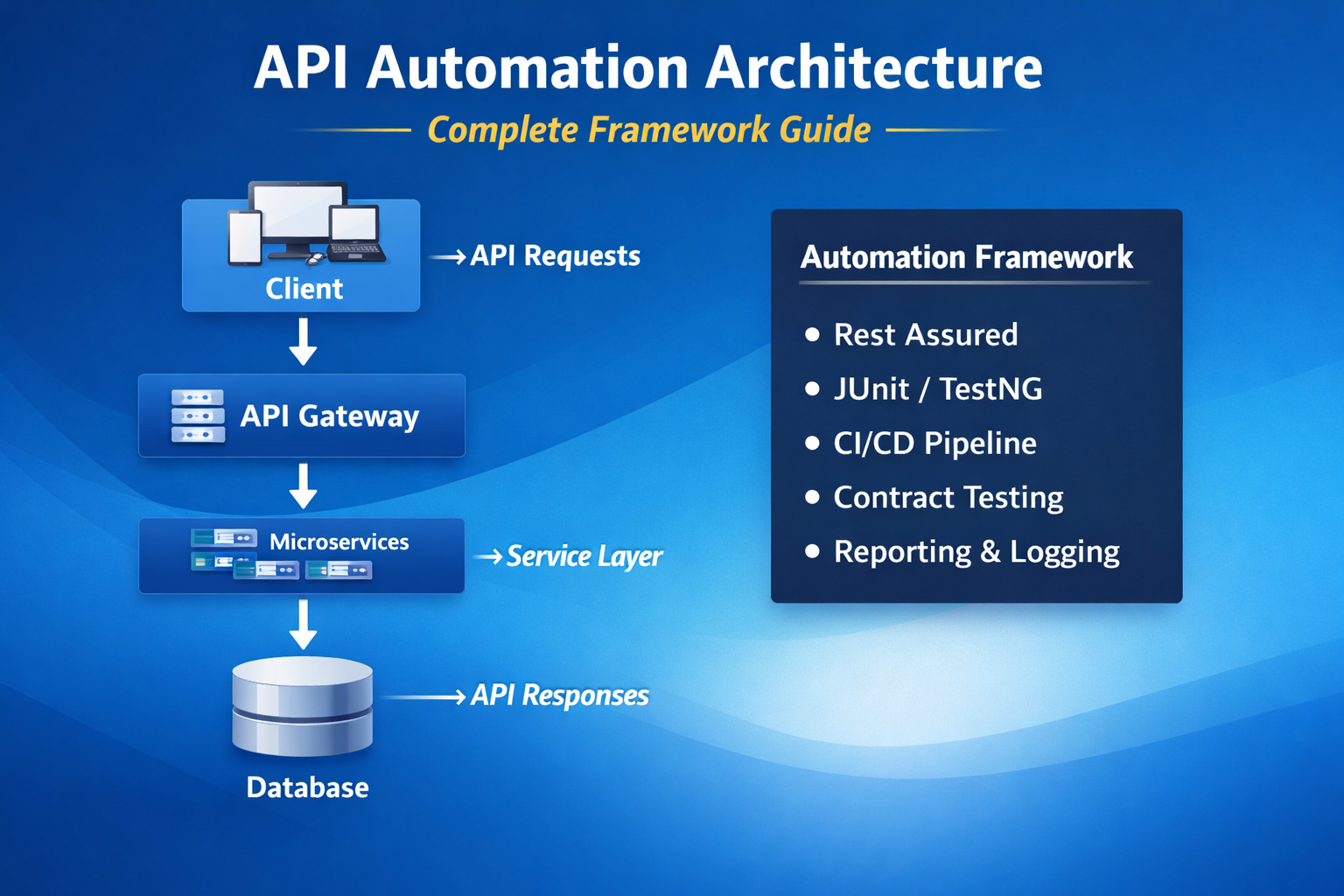
Modern applications rely heavily on APIs. From microservices to mobile apps, everything talks through APIs. But before any API allows access to data, it verifies identity and permissions. That is where API authentication comes in.
This comprehensive guide explains:
- What API authentication is
- Why authentication is critical in automation testing
- Basic Authentication
- API Key Authentication
- JWT (JSON Web Token) Authentication
- OAuth 2.0 Authentication
- Practical examples using Rest Assured
- Automation framework design for authentication handling
- Real-world best practices
- Interview questions and answers
By the end of this article, you will not just understand API authentication — you will be able to implement and explain it confidently in interviews.
What is API Authentication?
API authentication is the process of verifying the identity of a client attempting to access an API.
Before a server processes a request, it checks:
- Who is making the request?
- Are they authorized?
- Do they have permission to access this resource?
Without authentication, APIs are exposed to:
- Data breaches
- Unauthorized access
- Injection attacks
- Identity spoofing
In automation testing, authentication becomes even more important because:
- Most APIs are protected
- You cannot test endpoints without valid credentials
- Token management must be automated
- Expired sessions must be handled programmatically
Why API Authentication Matters for Testers?
As a tester, you must:
- Validate correct authentication behavior
- Test positive and negative scenarios
- Verify unauthorized access handling
- Automate token generation
- Validate token expiry
- Handle multi-role access
Example scenarios you must test:
- Access API with valid credentials → 200 OK
- Access API with invalid credentials → 401 Unauthorized
- Access with expired token → 401
- Access restricted endpoint → 403 Forbidden
Interview tip: If you only know how to send requests but don’t understand authentication flows, you are not ready for senior-level API automation roles.
Types of API Authentication
There are four major authentication mechanisms you must master:
- Basic Authentication
- API Key Authentication
- JWT (JSON Web Token) Authentication
- OAuth 2.0 Authentication
Let’s break them down in depth.
1. Basic Authentication
Basic Authentication is the simplest authentication mechanism.
The client sends:
Authorization: Basic base64(username:password)
The server decodes and validates credentials.
How It Works?
- Client encodes username and password in Base64
- Sends it in Authorization header
- Server decodes and validates
Example:
Username: admin
Password: password123
Encoded: YWRtaW46cGFzc3dvcmQxMjM=
Header:
Authorization: Basic YWRtaW46cGFzc3dvcmQxMjM=
Rest Assured Example
given()
.auth().basic("admin", "password123")
.when()
.get("/users")
.then()
.statusCode(200);
When to Use Basic Authentication?
- Internal systems
- Legacy applications
- Temporary testing environments
Limitations:
- Credentials sent with every request
- Not secure without HTTPS
- Not scalable
- Not suitable for modern applications
2. API Key Authentication
API Key authentication uses a unique key assigned to the client.
The key is sent:
- In header
OR - In query parameter
Example:
x-api-key: 1234567890abcdef
How It Works?
- Client receives API key during registration
- Client sends API key in every request
- Server validates key against database
Rest Assured Example
given()
.header("x-api-key", "1234567890abcdef")
.when()
.get("/orders")
.then()
.statusCode(200);
Advantages:
- Easy to implement
- Lightweight
- Stateless
Limitations:
- No user identity verification
- Key leakage risk
- Not suitable for complex authorization
- Cannot represent user roles
3. JWT (JSON Web Token) Authentication
JWT is one of the most popular authentication mechanisms in modern applications.
JWT stands for JSON Web Token.
It is:
- Stateless
- Secure
- Compact
- Digitally signed
Structure of JWT
JWT has three parts:
Header.Payload.Signature
Example:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.
eyJ1c2VySWQiOjEyMywicm9sZSI6IkFkbWluIn0.
SflKxwRJSMeKKF2QT4fwpMeJf36POk6yJV_adQssw5c
Header
Contains algorithm type.
Payload
Contains claims like:
- userId
- role
- expiration
Signature
Ensures token integrity.
JWT Authentication Flow
- Client sends login request
- Server validates credentials
- Server generates JWT
- Client stores JWT
- Client sends JWT in header:
Authorization: Bearer <token>
Rest Assured JWT Example
Step 1: Generate Token
String token =
given()
.contentType("application/json")
.body("{\"username\":\"admin\",\"password\":\"admin123\"}")
.when()
.post("/login")
.then()
.extract()
.path("token");
Step 2: Use Token
given()
.header("Authorization", "Bearer " + token)
.when()
.get("/profile")
.then()
.statusCode(200);
Why JWT is Powerful?
- Stateless authentication
- No session storage
- Scalable
- Works well in microservices
Testing JWT Scenarios:
- Valid token → 200
- Expired token → 401
- Modified token → 401
- Wrong signature → 401
- Missing token → 401
4. OAuth 2.0 Authentication
OAuth 2.0 is an authorization framework, not just authentication.
It is widely used in:
- Enterprise systems
- Banking applications
- Social login
- Cloud platforms
OAuth 2.0 uses access tokens instead of credentials.
OAuth 2.0 Roles:
- Resource Owner
- Client
- Authorization Server
- Resource Server
OAuth 2.0 Grant Types:
- Authorization Code
- Client Credentials
- Password Grant
- Refresh Token
Client Credentials Flow (Common in API Testing)
- Client sends client_id and client_secret
- Authorization server returns access token
- Client uses token to access API
Rest Assured OAuth Example:
String accessToken =
given()
.contentType("application/x-www-form-urlencoded")
.formParam("grant_type", "client_credentials")
.formParam("client_id", "client-id")
.formParam("client_secret", "client-secret")
.when()
.post("/oauth/token")
.then()
.extract()
.path("access_token");
Then use:
given()
.header("Authorization", "Bearer " + accessToken)
.when()
.get("/secure-data")
.then()
.statusCode(200);
Comparison: Basic vs API Key vs JWT vs OAuth 2.0
| Feature | Basic | API Key | JWT | OAuth 2.0 |
|---|---|---|---|---|
| Security | Low | Medium | High | Very High |
| Stateless | No | Yes | Yes | Yes |
| Enterprise Use | No | Limited | Yes | Yes |
| Role Support | No | No | Yes | Yes |
| Token Expiry | No | No | Yes | Yes |
Designing API Authentication in Automation Framework:
Now comes the real engineering part.
You should NEVER:
- Hardcode tokens
- Hardcode passwords
- Regenerate token in every test
Instead, build a centralized authentication utility.
Framework Design Best Practice:
Create:
- AuthManager class
- TokenCache utility
- Config reader
- Environment-based credential management
Example Structure:
src
├── config
├── auth
│ ├── AuthManager.java
│ ├── TokenService.java
├── tests
├── utils
AuthManager Example:
public class AuthManager { private static String token; public static String getToken() {
if (token == null || isExpired(token)) {
token = generateToken();
}
return token;
}
}
This ensures:
- Token reuse
- Reduced API calls
- Faster execution
- Clean design
Security Best Practices for Testers:
- Never commit secrets to Git
- Use environment variables
- Mask tokens in logs
- Use HTTPS only
- Validate 401 and 403 properly
- Test token expiry behavior
Common Interview Questions[FAQ]
What is difference between JWT and OAuth 2.0?
JWT is a token format.
OAuth 2.0 is an authorization framework.
OAuth may use JWT as token.
How do you automate OAuth 2.0 in Rest Assured?
Use client credentials flow to fetch access token, then reuse in header.
How do you handle expired tokens in automation?
Implement token validation and refresh mechanism in AuthManager.
Which authentication is most secure?
OAuth 2.0 with proper implementation and token validation.
Real-World Testing Scenarios:
- Multi-role testing (Admin, User, Guest)
- Role-based authorization validation
- Token tampering validation
- Expired token testing
- Performance impact of authentication
Final Thoughts:
API authentication is not just a concept — it is a core skill for modern automation engineers.
If you master:
- Basic Auth
- API Key
- JWT
- OAuth 2.0
- Token management in frameworks
You move from junior-level scripting to senior-level automation engineering.
Strong API authentication knowledge:
- Improves framework design
- Reduces flaky tests
- Improves security validation
- Boosts interview confidence
- Makes you enterprise-ready
Reference Links :
OAuth 2.0 Authorization Framework – RFC 6749
Have a look on Testng related Blog TestNG Automation Framework – Complete Architect Guide for Enterprise CI/CD & Parallel Execution
Have a look on Cucumber related Blog For a complete BDD implementation guide, read our Cucumber Automation Framework – Complete Beginner to Advanced Guide.
Have a look on Top 55 Best Java Interview Questions and Answers (With Code Examples) – Complete Guide for 2026
Have a look on Top Playwright Interview Questions and Ultimate Complete Guide for Automation Engineers